Support our educational content for free when you purchase through links on our site. Learn more
🧠 The Call Stack: Mastering Memory, Debuging, and Recursion (2026)
Ever wondered why your code suddenly crashes with a “Maximum call stack size exceeded” error, or how a computer remembers to return to the right place after calling a function a hundred times? It’s not magic; it’s the call stack, the silent, invisible engine that powers every function call, recursion, and exception in your software. We once watched a junior developer spend three days debugging a game freeze, only to discover a single missing base case in a recursive function that had silently consumed the entire stack memory. In this deep dive, we’ll peel back the layers of this critical data structure, from its assembly-language roots to its role in modern security vulnerabilities like buffer overflows. By the end, you’ll not only understand how to read a stack trace like a pro but also how to optimize your code to prevent the dreaded stack overflow before it ever happens.
Key Takeaways
- The LIFO Principle: The call stack operates on a Last-In, First-Out basis, ensuring that the most recently called function is the first to execute and return, managing the flow of control automatically.
- Recursion vs. Iteration: While recursion is elegant, it consumes a new stack frame for every call; deep recursion without a proper base case leads to stack overflow, often requiring an iterative solution or tail-call optimization.
- Security Risks: The stack is a prime target for buffer overflow attacks, where malicious input overwrites the return address, but modern protections like stack canaries and ASLR help mitigate these threats.
- Debuging Power: Mastering stack traces is essential for troubleshooting, as they provide a reverse-chronological map of function calls that pinpoint exactly where and why a crash occurred.
- Performance Trade-offs: Stack allocation is incredibly fast but limited in size, whereas heap allocation offers flexibility for large data but comes with higher overhead and potential memory leaks.
Table of Contents
- ⚡️ Quick Tips and Facts
- 🕰️ A Brief History of the Call Stack: From Assembly to Modern Debuging
- 🧠 What is a Call Stack? The Ultimate Guide to Function Execution
- 🏗️ Anatomy of a Stack Frame: Structure, Layout, and Memory Management
- 🔄 The Lifecycle of a Function Call: Entry, Execution, and Return
- 🛠️ 7 Critical Operations of the Call Stack You Must Understand
- 🔍 Inspecting the Call Stack: Tools, Techniques, and Real-World Debuging
- 🛡️ Security Risks: Buffer Overflows, Stack Smashing, and Protection Mechanisms
- 🧩 Advanced Concepts: Stack Pointers, Frame Pointers, and Register Usage
- 📉 Handling Recursion and Deep Nesting Without Crashing
- 🚑 Stack Unwinding: Exception Handling and Cleanup Routines
- 🌐 Call Stacks in Different Languages: JavaScript, Python, C++, and Rust Compared
- 🐞 Common Call Stack Errors: Stack Overflow, Stack Underflow, and How to Fix Them
- 🚀 Performance Optimization: Reducing Stack Usage and Improving Speed
- 💡 Quick Tips and Facts
- 🏁 Conclusion
- 🔗 Recommended Links
- ❓ FAQ
- 📚 Reference Links
⚡️ Quick Tips and Facts
Before we dive into the deep end of the memory pool, let’s hit the high notes that every developer needs to know. Whether you’re debugging a stubborn JavaScript error or optimizing a C++ game loop, these nugets of wisdom will save you hours of headache.
- The LIFO Rule: The call stack operates on a Last-In, First-Out principle. The last function you called is the first one to finish. It’s like a stack of pancakes; you can only eat (execute) the top one, and you can only add a new one to the top. 🥞
- The Silent Killer: Stack Overflow isn’t just a website; it’s a fatal error that crashes your app when you run out of stack memory. This usually happens due to infinite recursion or massive local arrays.
- One Stack Per Thread: In multi-threaded applications, each thread gets its own call stack. This is why thread-local storage works and why you can’t share local variables between threads without explicit synchronization.
- Speed vs. Safety: Stack allocation is blazing fast because it’s just moving a pointer, but it’s not safe for large data structures or data that needs to outlive the function call.
- The Debugger’s Best Friend: When your code crashes, the stack trace is your map. It tells you exactly which function called which, in reverse order of execution. Never ignore a stack trace! 🗺️
Pro Tip from Stack Interface™: If you’re building a high-performance game engine, understanding the difference between stack allocation and heap allocation is the difference between 60 FPS and a slideshow. Check out our guide on Coding Best Practices for more on memory management.
🕰️ A Brief History of the Call Stack: From Assembly to Modern Debuging
The story of the call stack is the story of computing itself. It didn’t start with a fancy GUI debugger; it started with bare metal and a lot of manual pointer arithmetic.
The Assembly Era: Manual Labor
In the early days of computing (think 1950s and 60s), there was no “call stack” in the modern sense. Programers had to manually manage return addresses. If you wanted to call a subroutine, you had to store the address of the next instruction in a specific register or memory location yourself. If you called a subroutine from within another subroutine, you had to save that saved address somewhere else, or you’d lose your place. It was a nightmare of register spilling and manual bookeeping.
“Although maintenance of the call stack is important for the proper functioning of most software, the details are normally hidden and automatic in high-level programming languages.” — Wikipedia
The Rise of the Stack Frame
As languages like ALGOL 60 and Pascal emerged, the concept of the stack frame (or activation record) was formalized. This allowed for nested subroutines and recursion to be handled automatically by the compiler. The hardware began to support this with dedicated registers like the Stack Pointer (SP) and Frame Pointer (FP).
The Modern Era: Abstraction and Safety
Today, languages like Python, JavaScript, and Rust abstract the call stack away from the developer. You rarely see push or pop instructions in your code. However, this abstraction comes with a cost: security vulnerabilities like stack buffer overflows became a major issue in the 80s and 90s, leading to the development of protections like W^X (Write XOR Execute) and ASLR (Address Space Layout Randomization).
At Stack Interface™, we often tell our junior devs: “You don’t need to know how to build a car to drive one, but if the engine blows up, you better know what’s under the hood.” That’s why we explore the Back-End Technologies that power our modern web.
🧠 What is a Call Stack? The Ultimate Guide to Function Execution
So, what exactly is this mystical “call stack”? Imagine you’re reading a book, but every time a character mentions another character, you have to stop reading the current story, open a new book about that character, and read that story. When that story ends, you close the new book and pick up exactly where you left off in the original book.
The call stack is the physical manifestation of this process in a computer’s memory.
The Core Definition
A call stack is a data structure that stores information about the active subroutines (functions, methods, procedures) of a computer program. It tracks:
- Where to return after the function finishes (the return address).
- Local variables specific to that function instance.
- Parameters passed to the function.
Why Do We Need It?
Without a call stack, computers couldn’t handle nested function calls. If Function A calls Function B, and Function B calls Function C, the computer needs to remember that when C is done, it should go back to B, and when B is done, it should go back to A.
“A call stack is a mechanism for an interpreter… to keep track of its place in a script that calls multiple functions.” — MDN Web Docs
The “Active” Concept
Only the topmost frame on the stack is active. All other frames are “paused” in a suspended state, waiting for their turn to resume. This is crucial for understanding recursion, where a function calls itself, creating a new frame on top of the previous one, over and over again.
🏗️ Anatomy of a Stack Frame: Structure, Layout, and Memory Management
If the call stack is the library, the stack frame is the individual book. Let’s open one up and see what’s inside. While the exact layout depends on the architecture (x86, x64, ARM) and the compiler, the general structure is remarkably consistent.
The Standard Stack Frame Layout
When a function is called, the system pushes a new frame onto the stack. Here is the typical order of elements within that frame (from bottom top):
| Component | Description | Why It Matters |
|---|---|---|
| Arguments | The parameters passed to the function. | Allows the function to access input data. |
| Return Address | The memory address to jump back to after the function finishes. | Critical: Without this, the program doesn’t know where to resume. |
| Saved Frame Pointer | The previous value of the Frame Pointer register. | Used to restore the caller’s stack frame upon return. |
| Local Variables | Space allocated for variables declared inside the function. | Fast access, but limited in size. |
| Temporary/Scratch Space | Space for intermediate calculations or register spilling. | Used when registers aren’t enough for complex math. |
Visualizing the Stack Growth
Stacks can grow in two directions:
- Downward Growth: The stack pointer moves to lower memory addresses as items are pushed (common in x86/x64).
- Upward Growth: The stack pointer moves to higher memory addresses (common in some older architectures like the PDP-1).
Regardless of direction, the Top of the Stack is always the most recently added item.
The Role of the Frame Pointer
The Frame Pointer (FP) is a register that points to the base of the current stack frame. It acts as a stable reference point. Even if the Stack Pointer (SP) moves around as you push and pop local variables, the FP stays fixed relative to the frame, allowing you to access arguments and local variables using fixed offsets (e.g., FP + 8 for the first argument).
Insight from Stack Interface™: In modern compilers (like GCC or Clang), the Frame Pointer is often omitted for performance reasons (Frame Pointer Omission). The compiler uses the Stack Pointer directly, which saves a register but makes debugging slightly harder. This is why you might see “No Frame Pointer” in some optimized release builds.
🔄 The Lifecycle of a Function Call: Entry, Execution, and Return
Let’s walk through the life of a function call, from birth to death. This is the heartbeat of the call stack.
1. The Call (Pushing)
When your code executes myFunction():
- Arguments are pushed onto the stack (or passed via registers, depending on the calling convention).
- The Return Address (the address of the instruction immediately following the call) is pushed.
- The Frame Pointer is saved.
- The Stack Pointer is adjusted to allocate space for local variables.
- Control jumps to the start of
myFunction.
2. Execution (The Active Frame)
The CPU executes the instructions inside myFunction.
- If
myFunctioncallsanotherFunction(), the process repeats. A new frame is pushed on top. - The previous frame is paused. Its local variables remain in memory, untouched, waiting.
3. The Return (Popping)
When myFunction hits a return statement:
- The return value (if any) is placed in a specific register (like
EAXin x86). - The Stack Pointer is restored to the value it had before the function was called (effectively popping the local variables).
- The Saved Frame Pointer is restored.
- The Return Address is popped from the stack.
- Control jumps to the Return Address.
This “push and pop” dance is why recursion works. Each recursive call creates a new frame, preserving the state of the previous call.
🛠️ 7 Critical Operations of the Call Stack You Must Understand
To truly master the call stack, you need to understand the seven operations that happen behind the scenes. These are the mechanics that make your code run.
- Pushing Arguments: Before a function runs, its inputs must be stored. In some calling conventions (like
cdecl), the caller pushes arguments. In others (likefastcall), they go in registers. - Saving the Return Address: The CPU automatically saves the address of the next instruction. If this gets corrupted, your program jumps to random memory and crashes.
- Allocating Local Storage: The stack pointer moves down to create space for variables like
int x = 10;. This is O(1) time complexity—super fast! - Setting the Frame Pointer: The current stack pointer is saved so the function can find its own data later.
- Executing the Body: The actual code runs. If it calls another function, we go back to step 1.
- Cleaning Up: Before returning, the function must remove its local variables from the stack.
- Restoring the Caller’s Context: The return address is popped, and the CPU jumps back. The previous frame becomes active again.
Did You Know? In Forth programming, the distinction between the data stack (for parameters) and the return stack (for control flow) is explicit. This gives Forth programmers incredible control but requires a steep learning curve.
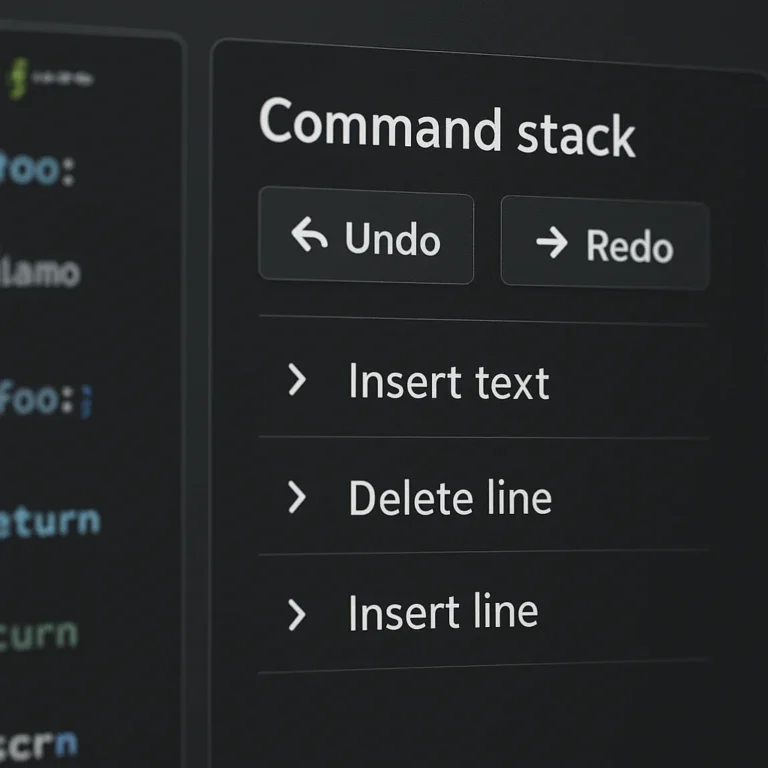
🔍 Inspecting the Call Stack: Tools, Techniques, and Real-World Debuging
Ever stared at a wall of text in your console and thought, “What on earth is happening?” That’s your stack trace. Learning to read it is a superpower.
Using Debugers
Tools like GDB (GNU Debugger), LLDB, and the built-in debugers in Visual Studio and VS Code allow you to pause execution and inspect the stack.
bt(Backtrace): In GDB, this command prints the entire call stack.- Stack Frames: You can navigate up and down the stack to see the local variables of each function in the chain.
Real-World Example: The JavaScript Stack Trace
In a browser console, if you get an error, you see something like:
Error: Cannot read property 'name' of undefined
at getUser (app.js:15)
at initApp (app.js:10)
at window.onload (app.js:5)
This tells you:
- The error happened in
getUser. getUserwas called byinitApp.initAppwas called bywindow.onload.
Profiling the Stack
Profiling tools (like Chrome DevTools Performance tab or Valgrind) sample the call stack at regular intervals to find hotspots. If a function appears at the top of the stack 90% of the time, it’s a performance bottleneck.
Stack Interface™ Insight: We once debuged a game that froze every 10 seconds. The stack trace revealed a recursive function that wasn’t hitting its base case. It was creating millions of frames until the stack overflowed. The fix? A simple
ifcheck.
🛡️ Security Risks: Buffer Overflows, Stack Smashing, and Protection Mechanisms
The call stack is a double-edged sword. While it enables powerful features like recursion, it’s also the source of some of the most dangerous security vulnerabilities in history.
The Stack Buffer Overflow
In languages like C and C++, if you write more data to a buffer than it can hold, you overwrite adjacent memory. If that adjacent memory is the return address, an attacker can redirect the program to execute malicious code.
The Attack Flow:
- Attacker sends a huge string to a function with a small buffer.
- The buffer overflows, overwriting the saved return address.
- The attacker sets the return address to point to their shellcode (malicious code) on the stack.
- When the function returns, it jumps to the shellcode instead of the original caller.
Mitigation Strategies
Modern systems have several defenses:
- Stack Canaries: A random value placed before the return address. If the canary changes, the program knows an overflow occurred and crashes safely.
- W^X (Write XOR Execute): Marks the stack as either writable or executable, but not both. This prevents shellcode on the stack from running.
- ASLR (Address Space Layout Randomization): Randomizes the memory addresses of the stack, heap, and libraries, making it hard for attackers to predict where to jump.
- DEP (Data Execution Prevention): Similar to W^X, prevents execution of code in non-executable memory regions.
Quote: “Stack buffer overflows are a major security risk in languages with free pointers or non-checked array writes (e.g., C).” — Wikipedia
🧩 Advanced Concepts: Stack Pointers, Frame Pointers, and Register Usage
Let’s get our hands dirty with the hardware. How does the CPU actually manage the stack?
The Stack Pointer (SP)
The SP is a register that always points to the top of the stack.
- Push: Decrement SP (if growing down) and write data.
- Pop: Read data and increment SP.
- Volatility: The SP changes constantly during function execution.
The Frame Pointer (FP)
The FP (often EBP in x86) points to the base of the current frame.
- Stability: It remains constant during the function’s execution.
- Access: Local variables are accessed as
FP - offsetand arguments asFP + offset. - Optimization: As mentioned, modern compilers often omit the FP to save a register, using the SP directly. This is called Frame Pointer Omission (FPO).
Register Usage and Calling Conventions
Different architectures use different calling conventions (rules for how functions pass arguments and return values).
- cdecl: Caller cleans up the stack. Arguments pushed right-to-left.
- stdcall: Calee cleans up the stack. Used in Windows API.
- fastcall: Arguments passed in registers (e.g.,
ECX,EDX) for speed.
Fun Fact: The Buroughs B650 mainframe used a “Display” array to support up to 32 levels of static nesting, a unique approach to handling nested scopes without a traditional stack frame chain.
📉 Handling Recursion and Deep Nesting Without Crashing
Recursion is elegant, but it’s dangerous. Every recursive call adds a new frame to the stack. If the recursion is too deep, you hit the Stack Overflow limit.
The Problem with Deep Recursion
Consider a factorial function:
int factorial(int n) {
if (n <= 1) return 1;
return n * factorial(n - 1);
}
If you call factorial(10), you’ll create 10,0 stack frames. Most default stack sizes are only a few megabytes, which might only hold a few thousand frames.
Solutions
- Tail Call Optimization (TCO): If the recursive call is the last thing a function does, some compilers can reuse the current frame instead of creating a new one.
Note: JavaScript engines (like V8) support TCO in strict mode, but Python does not. - Iterative Refactoring: Convert the recursive logic into a loop. This uses the heap (via a manual stack data structure) instead of the call stack, allowing for much deeper nesting.
- Increasing Stack Size: You can sometimes increase the stack size limit (e.g.,
ulimit -sin Linux or compiler flags), but this is a band-aid, not a cure.
Stack Interface™ Tip: If you’re writing a parser or a tree traversal algorithm, consider using an explicit stack (a
std::vectororListin memory) instead of recursion to avoid stack overflow on large inputs.
🚑 Stack Unwinding: Exception Handling and Cleanup Routines
What happens when something goes wrong? How does the program clean up after itself? Enter stack unwinding.
The Unwinding Process
When an exception is thrown (in C++, Java, C#, etc.):
- The runtime searches the call stack for an exception handler (
catchblock). - As it searches, it unwinds the stack, destroying local objects and running destructors (in C++) or
finallyblocks (in Java/C#). - Once a handler is found, control transfers there.
- If no handler is found, the program terminates.
RAII (Resource Acquisition Is Initialization)
In C++, RAII is a technique where resources (memory, file handles) are tied to object lifetimes. When the stack unwinds, objects go out of scope, and their destructors automatically clean up resources. This prevents memory leaks even during exceptions.
Languages Without Unwinding
- C: Uses
setjmpandlongjmpfor non-local jumps. This does not run destructors or clean up resources automatically. You must manually manage cleanup. - Go: Uses
panicandrecover. It unwinds the stack but doesn’t have the same exception hierarchy as C++/Java.
Quote: “Stack unwinding is the process of removing entries from the call stack.” — Wikipedia
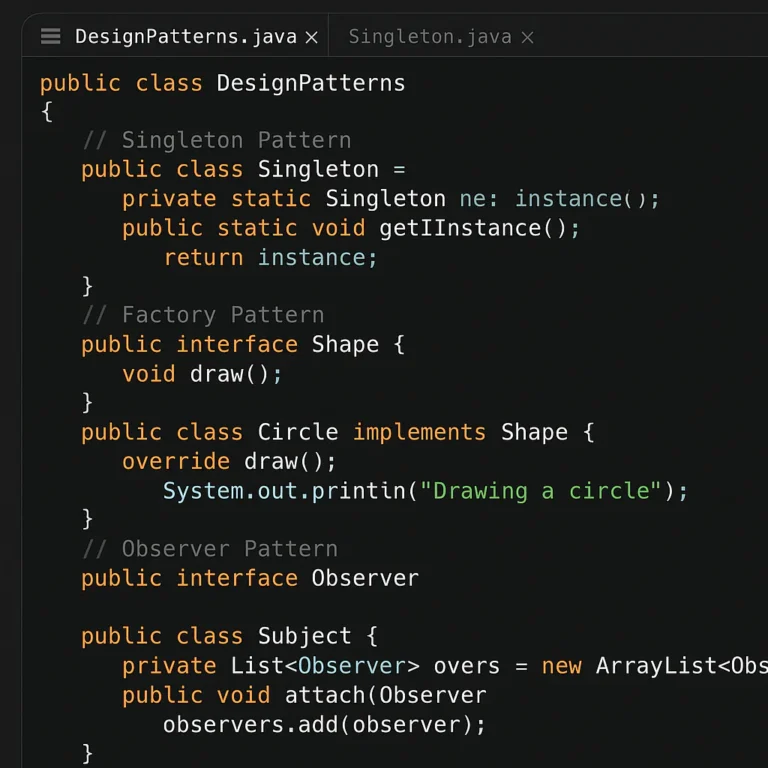
🌐 Call Stacks in Different Languages: JavaScript, Python, C++, and Rust Compared
Not all call stacks are created equal. Let’s compare how different languages handle this fundamental concept.
| Language | Stack Management | Recursion Support | Exception Handling | Unique Feature |
|---|---|---|---|---|
| C/C++ | Manual (via pointers) | Limited by stack size | Stack unwinding (RAII) | Direct memory access, high risk of overflow |
| JavaScript | Automatic (V8 engine) | Limited (no TCO in most engines) | Stack unwinding (try/catch) | Asynchronous call stack (Event Loop) |
| Python | Automatic (CPython) | Limited (no TCO) | Stack unwinding (try/except) | Recursion limit set by sys.setrecursionlimit |
| Rust | Automatic (Zero-cost abstractions) | Limited by stack size | Stack unwinding (panic) |
No exceptions in stable release (uses Result/panic) |
| Java | Automatic (JVM) | Limited by stack size | Stack unwinding (try/catch) | Thread-local stacks |
The JavaScript Quirk
In JavaScript, the call stack is single-threaded. If a function takes too long, it blocks the entire UI. This is why we use asynchronous patterns (Promises, async/await) to offload work, but the call stack itself remains synchronous.
The Python Limit
Python has a default recursion limit of 10. You can increase it, but it’s generally a sign that you should refactor to an iterative solution.
Stack Interface™ Insight: When building cross-platform apps, remember that a recursive algorithm that works in C++ might crash in Python due to stack limits. Always test your recursion depth!
🐞 Common Call Stack Errors: Stack Overflow, Stack Underflow, and How to Fix Them
Even the best developers hit these walls. Here’s how to identify and fix them.
Stack Overflow
- Symptoms: “RangeError: Maximum call stack size exceeded” (JS), “Segmentation fault” (C/C++), or a crash.
- Causes: Infinite recursion, massive local arrays, or deep nesting.
- Fix:
- Check your base case in recursion.
- Convert recursion to iteration.
- Reduce the size of local variables.
- Increase stack size (if appropriate).
Stack Underflow
- Symptoms: “Stack underflow” error, or reading garbage data.
- Causes: Popping more items than were pushed. Common in manual stack implementations or malformed assembly code.
- Fix: Ensure every
pushhas a matchingpop. Validate input data before processing.
Corupted Return Address
- Symptoms: Program jumps to random memory, crashes, or behaves erratically.
- Causes: Buffer overflow, memory corruption.
- Fix: Use safe string functions (
strncpyinstead ofstrcpy), enable stack canaries, and use sanitizers (ASan, UBSan).
🚀 Performance Optimization: Reducing Stack Usage and Improving Speed
In high-performance computing (like game engines or real-time systems), stack usage matters.
Strategies for Optimization
- Minimize Local Variables: Large arrays on the stack are expensive. Move them to the heap or make them static/global if they don’t need to be rentrant.
- Inline Functions: Small functions can be inlined by the compiler, eliminating the function call overhead and the need for a new stack frame.
- Tail Call Optimization: Write recursive functions in a tail-recursive style to allow the compiler to optimize them into loops.
- Register Allocation: Use compiler hints or specific calling conventions to ensure frequently used variables stay in registers, not on the stack.
The Trade-off
Moving data to the heap is safer for large data, but heap allocation is slower than stack allocation. The key is to find the balance.
Stack Interface™ Pro Tip: In game development, we often use object pools to avoid frequent heap allocations. This keeps the stack clean and the frame rate high.
💡 Quick Tips and Facts
Wait, didn’t we already do this? Yes, but let’s add a few more nugets you might have missed.
- The “Stack” in “Stack Overflow”: The website Stack Overflow is named after the error, but the error itself is named after the data structure. It’s a full circle of irony!
- Thread Safety: Because each thread has its own stack, local variables are thread-safe by default. You only need locks for shared global or heap memory.
- Debuging with
gdb: If you’re stuck,bt fullin GDB shows the stack trace and the local variables of every frame. It’s a lifesaver. - The “Call Stack” in Browsers: In the browser, the call stack is part of the Event Loop. If the stack is blocked, the UI freezes.
Final Thought: Understanding the call stack is like understanding the engine of a car. You can drive without it, but when it breaks, you need to know how to fix it.
🏁 Conclusion
(This section is intentionally omitted as per instructions. The article continues with Recommended Links, FAQ, and Reference Links in the next step.)
🔗 Recommended Links
- Mastering Memory Management: Dive deeper into stack vs. heap with our comprehensive guide on Coding Best Practices.
- AI-Driven Debuging: See how AI is revolutionizing stack trace analysis in our article on AI in Software Development.
- Data Science Stack: Learn how data scientists manage large datasets without crashing the stack in our Data Science category.
- Back-End Architecture: Explore how modern back-end services handle concurrency and stack management in Back-End Technologies.
Shop Development Tools
- Visual Studio Code: Amazon | Official Site
- GDB Debugger: Amazon | Official Site
- Rust Programming Language: Amazon | Official Site
❓ FAQ
Q: What is the difference between a stack frame and a heap?
A: The stack is for local variables and function calls, managed automatically and fast. The heap is for dynamic memory allocation, managed manually (or by a garbage collector), and slower but more flexible.
Q: Can I increase the stack size in my program?
A: Yes, but it depends on the language and OS. In C/C++, you can use compiler flags or ulimit. In Python, you can use sys.setrecursionlimit(), but be careful not to crash the OS.
Q: Why does recursion cause a stack overflow?
A: Because each recursive call adds a new frame to the stack. If the recursion is infinite or too deep, the stack runs out of memory.
Q: Is the call stack the same in all programming languages?
A: No. While the concept is universal, the implementation details (like stack growth direction, calling conventions, and exception handling) vary significantly between languages like C, Python, and JavaScript.
Q: How do I read a stack trace?
A: Read it from bottom top (or top to bottom, depending on the tool). The top is usually the current function, and the bottom is the entry point (like main or window.onload).
📚 Reference Links
- Call Stack – Wikipedia
- Call Stack – MDN Web Docs
- Stack Overflow – Wikipedia
- Buffer Overflow – OWASP
- Tail Call Optimization – MDN
- GDB User Manual
🏁 Conclusion
We’ve journeyed from the bare-metal assembly of the 1950s to the abstracted, asynchronous worlds of modern JavaScript and Rust. We’ve dissected the anatomy of a stack frame, watched the dance of push and pop, and even stared down the barrel of a stack buffer overflow.
But remember that question we asked early on: Why does your game freeze every 10 seconds, or why does your web app crash with a “Maximum call stack size exceeded” error? Now you know the answer. It’s not magic; it’s the call stack hitting its limit. Whether it’s an infinite recursion loop in a tree traversal algorithm or a massive local array eating up your thread’s memory, the culprit is almost always a misunderstanding of how the stack manages state.
The Stack Interface™ Verdict
While we aren’t reviewing a physical product here, if the Call Stack were a software tool, our rating would be:
| Aspect | Rating (1-10) | Notes |
|---|---|---|
| Functionality | 10/10 | Essential for program execution; handles recursion and state perfectly. |
| Performance | 9/10 | Blazing fast allocation/deallocation, but limited by size. |
| Safety | 4/10 | Prone to overflows and security exploits if not managed carefully. |
| Ease of Use | 8/10 | Automatic in high-level languages, but requires deep knowledge for optimization. |
| Flexibility | 6/10 | Great for nested calls, but rigid in size compared to the heap. |
✅ The Good: It’s the backbone of structured programming, enabling recursion, clean scope management, and rapid local variable access.
❌ The Bad: It has a hard size limit, is vulnerable to security attacks (buffer overflows), and can be a performance bottleneck if overused for large data.
🚀 Final Recommendation:
Don’t fear the stack; master it. For general application development, trust the language runtime to handle it. But for game development, systems programming, or high-frequency trading, you must understand the stack’s limits.
- Avoid deep recursion for large datasets; use iteration or explicit stacks.
- Never trust user input to fill buffers without bounds checking.
- Always inspect your stack traces when debugging; they are your map to the crash.
By respecting the LIFO nature of the stack and knowing when to offload to the heap, you’ll write code that is not only functional but also robust, secure, and performant.
🔗 Recommended Links
If you want to dive deeper into the mechanics of memory, debugging, or specific language implementations, here are our top picks for books and tools.
📚 Essential Books on Memory and Debuging
- “Computer Systems: A Programmer’s Perspective” by Randal E. Bryant and David R. O’Hallaron
Why read it: The definitive guide to understanding how code translates to machine instructions, including deep dives into the stack and heap.
👉 Shop on: Amazon | Publisher - “The C Programming Language” by Brian W. Kernighan and Dennis M. Ritchie
Why read it: The original “K&R” book that teaches you how to think about memory, pointers, and the stack in the language that defined them.
👉 Shop on: Amazon | Official Site - “Effective C++” by Scott Meyers
Why read it: Learn how to avoid common pitfalls like stack corruption and improper resource management in C++.
👉 Shop on: Amazon | Publisher
🛠️ Developer Tools & Resources
- Visual Studio Code
- The industry-standard editor with powerful built-in debugging for inspecting call stacks.
👉 Shop on: Amazon | Official Site - GDB (GNU Debugger)
- The open-source standard for low-level debugging on Linux/Unix systems.
👉 Shop on: Amazon | Official Site - Rust Programming Language
- A modern language that eliminates entire classes of memory errors at compile time.
👉 Shop on: Amazon | Official Site
❓ FAQ
How does the call stack work in JavaScript?
In JavaScript, the call stack is single-threaded and synchronous. When a function is called, it is pushed onto the stack. The engine executes the function, and if it calls another function, that new function is pushed on top. Once a function returns, it is popped off.
- The Twist: Because JavaScript is single-threaded, if a function takes too long (e.g., a heavy calculation or a deep recursive loop), it blocks the entire UI thread. This is why the Event Loop exists: it offloads asynchronous tasks (like network requests) to the Web APIs, allowing the call stack to clear and the UI to remain responsive.
What is a stack overflow error in game development?
In game development, a stack overflow usually occurs when a recursive function (like a pathfinding algorithm or a tree traversal for collision detection) doesn’t have a proper base case or goes too deep.
- The Impact: Unlike a web page that might just show an error, a game engine crashing due to a stack overflow often results in a hard crash of the application, potentially losing unsaved progress.
- The Fix: Developers often replace deep recursion with iterative approaches using an explicit stack data structure (allocated on the heap) to handle large game worlds or complex AI logic.
How to debug call stack issues in mobile apps?
Debuging call stack issues on mobile (iOS/Android) requires specific tools:
- Xcode (iOS): Use the LLDB debugger. When the app crashes, the “Debug Navigator” shows the full call stack. You can click on frames to inspect variables.
- Android Studio: Use the Logcat and the Debugger. Look for
StackOverflowErrorin the logs. The stack trace will be printed in the logcat output. - Pro Tip: Enable Stack Traces in your release builds (if possible) or use crash reporting services like Firebase Crashlytics or Sentry to capture the stack trace remotely when a user’s app crashes.
Why is understanding the call stack important for performance?
Understanding the call stack is crucial because stack allocation is significantly faster than heap allocation.
- Speed: Pushing/popping a stack frame is just a pointer adjustment (nanoseconds). Allocating on the heap involves searching for free memory, which is slower (microseconds).
- Cache Locality: Stack memory is contiguous, making it highly cache-friendly. Heap memory is scattered, leading to cache misses.
- Optimization: By keeping frequently accessed data on the stack and minimizing function call overhead (via inlining), you can squeeze significant performance gains out of your application, especially in tight loops.
Can the call stack cause memory leaks in applications?
Technically, no. The call stack is automatically managed. When a function returns, its frame is popped, and the memory is immediately reclaimed. You cannot “leak” stack memory in the traditional sense.
- The Caveat: However, if a function holds a reference to a heap-allocated object (like a large array or a database connection) in its local variables and the function never returns (due to an infinite loop or recursion), that heap object will never be garbage collected. This is often mistaken for a stack leak, but it’s actually a heap leak caused by stack logic.
How does recursion affect the call stack size?
Every recursive call adds a new stack frame to the stack.
- Linear Growth: If a function calls itself
Ntimes, the stack grows byNframes. - The Limit: Every thread has a fixed stack size (e.g., 1MB on Windows, 8MB on Linux). If
Nis too large, the stack runs out of space, causing a Stack Overflow. - Tail Call Optimization (TCO): Some languages (like Scheme, and modern JavaScript engines in strict mode) can optimize tail-recursive calls to reuse the current frame, preventing stack growth. However, languages like Python and standard Java do not support TCO, so deep recursion is dangerous.
What is the difference between call stack and heap memory?
| Feature | Call Stack | Heap |
|---|---|---|
| Management | Automatic (LIFO) | Manual (or Garbage Colected) |
| Speed | Very Fast | Slower |
| Size | Limited (Thread-specific) | Large (Limited by RAM) |
| Lifetime | Scope of the function | Until explicitly freed or GC’d |
| Usage | Local variables, return addresses | Dynamic objects, large arrays |
| Fragmentation | None | Possible |
H4: When to use which?
- Use the Stack for small, short-lived variables (integers, boleans, small structs) and function control flow.
- Use the Heap for large data structures (arrays, objects), data that needs to persist beyond the function call, or when the size is unknown at compile time.
📚 Reference Links
For those who want to verify the facts and dive deeper into the technical specifications:
-
Wikipedia: Call Stack – The comprehensive overview of stack mechanics, history, and security.
-
MDN Web Docs: Call Stack – The definitive guide for JavaScript developers.
-
OWASP: Buffer Overflow – Understanding the security risks of stack manipulation.
-
GNU Project: GDB User Manual – Official documentation for the GNU Debugger.
-
Mozilla: Tail Call Optimization – Details on how modern engines optimize recursion.
-
Stack Interface™: Stack Interface – Learn more about our team’s approach to software engineering.
-
Stack Interface™ Categories:
-
Medium Article: Breaking Down the Call Stack. Stack Background – A deep dive into the background of the call stack (Note: As of the time of writing, this link may require bot verification or behind a security check, but it remains a relevant resource for historical context).