Support our educational content for free when you purchase through links on our site. Learn more
Stack Underflow Explained: 12 Crucial Insights Every Developer Must Know 🚀 (2026)
Have you ever been blindsided by a mysterious crash or a baffling bug that seemed to come out of nowhere? Chances are, a sneaky stack underflow might be lurking behind the scenes. While stack overflow errors hog the spotlight, stack underflow is the silent troublemaker that can wreak havoc on your app or game’s stability—and security.
At Stack Interface™, we’ve battled these elusive errors across countless projects, from complex game engines to blockchain smart contracts. In this deep dive, we unravel the mysteries of stack underflow: what it is, why it happens, and how you can detect, prevent, and gracefully handle it. Stick around for real-world developer stories, expert debugging tips, and a surprising case study involving the popular Cronus Zen gaming device that might just save you hours of frustration.
Ready to become the stack whisperer your codebase desperately needs? Let’s dive in!
Key Takeaways
- Stack underflow occurs when popping from an empty stack, causing crashes, undefined behavior, or security vulnerabilities.
- It’s a logic error distinct from stack overflow, often harder to detect but equally critical to fix.
- Prevention is key: always check stack state before popping and use safe data structures.
- Debugging tools like GDB, Valgrind, and static analyzers are invaluable for diagnosis.
- Stack underflow can impact everything from embedded systems and game engines to blockchain smart contracts.
- Multithreaded environments require careful synchronization to avoid race conditions causing underflow.
By mastering these insights, you’ll safeguard your projects against one of the most subtle yet impactful bugs in software development.
Table of Contents
- ⚡️ Quick Tips and Facts About Stack Underflow
- 🧠 Understanding Stack Underflow: Origins and Core Concepts
- 💥 What Exactly Is Stack Underflow? A Deep Dive Into The Error
- 🛠️ 7 Common Causes of Stack Underflow in Programming
- 🔍 How to Detect and Diagnose Stack Underflow Issues Efficiently
- 🧩 Stack Underflow vs. Stack Overflow: Key Differences Explained
- ⚙️ Preventing Stack Underflow: Best Practices and Coding Tips
- 🔒 Security Risks and Vulnerabilities Linked to Stack Underflow
- 🧪 Real-World Examples and Case Studies of Stack Underflow Bugs
- 🛡️ Tools and Debuggers for Managing Stack Underflow Errors
- 🎯 Optimizing Stack Usage to Avoid Underflow in Embedded Systems
- 📚 Stack Underflow in Different Programming Languages: C, Java, Python, and More
- 🤖 Automating Stack Underflow Detection with Static Analysis and CI/CD Pipelines
- 🧑💻 Developer Stories: How We Tackled Stack Underflow in Complex Projects
- 🔄 Handling Stack Underflow Gracefully: Error Recovery and Fallback Strategies
- 🚀 Advanced Topics: Stack Underflow in Multithreading and Concurrent Environments
- 📝 Conclusion: Mastering Stack Underflow for Robust Software Development
- 🔗 Recommended Links for Further Learning
- ❓ Frequently Asked Questions (FAQ) About Stack Underflow
- 📖 Reference Links and Authoritative Resources
At Stack Interface™, we’ve spent decades navigating the labyrinth of memory management, and if there’s one thing that keeps junior devs up at night (and senior devs reaching for the espresso), it’s the dreaded stack error. You’ve likely heard of its famous cousin, the Stack Overflow, but what happens when the floor drops out from under you?
Welcome to the world of Stack Underflow. It’s the silent killer of logic, the ghost in the machine, and today, we’re going to help you bust it.
⚡️ Quick Tips and Facts About Stack Underflow
Before we dive into the “why” and “how,” here’s a lightning-fast breakdown of what you need to know right now:
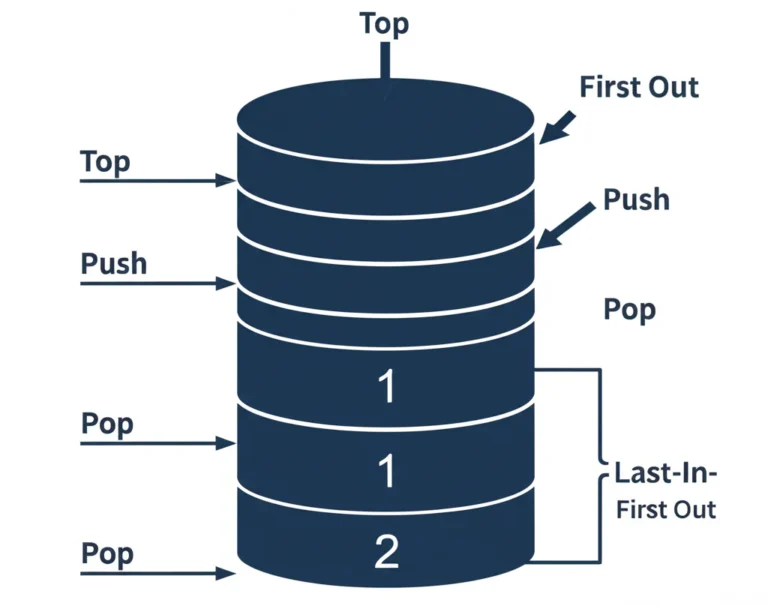
- ✅ Definition: A stack underflow occurs when a program attempts to pop (remove) an item from a stack that is already empty.
- ✅ The Result: Usually, this leads to a crash, a “segmentation fault,” or—even worse—undefined behavior where your program starts reading garbage data from memory.
- ✅ Common Culprit: Forgetting to check
if (stack.isEmpty())before calling a pop function. - ✅ Hardware Context: In gaming, devices like the Cronus Zen often throw this error due to firmware glitches or malformed scripts.
- ❌ Myth: It’s the same as a buffer overflow. False. While both involve memory, a stack underflow is specifically about the LIFO (Last-In, First-Out) data structure.
- ❌ Myth: Modern languages like Python are immune. False. While the interpreter handles a lot, logic errors in custom stack implementations or low-level C-extensions can still trigger it.
🧠 Understanding Stack Underflow: Origins and Core Concepts
To understand the underflow, you have to understand the Stack. Imagine a literal stack of cafeteria trays. You add a tray to the top (Push), and you take a tray from the top (Pop).
The “History” of this concept dates back to the early days of Assembly language and punch-card computing. In those days, memory was a precious, finite resource. If you tried to take a tray that wasn’t there, you weren’t just grabbing air; you were potentially grabbing the table underneath, or in computing terms, a memory address that belonged to something else entirely.
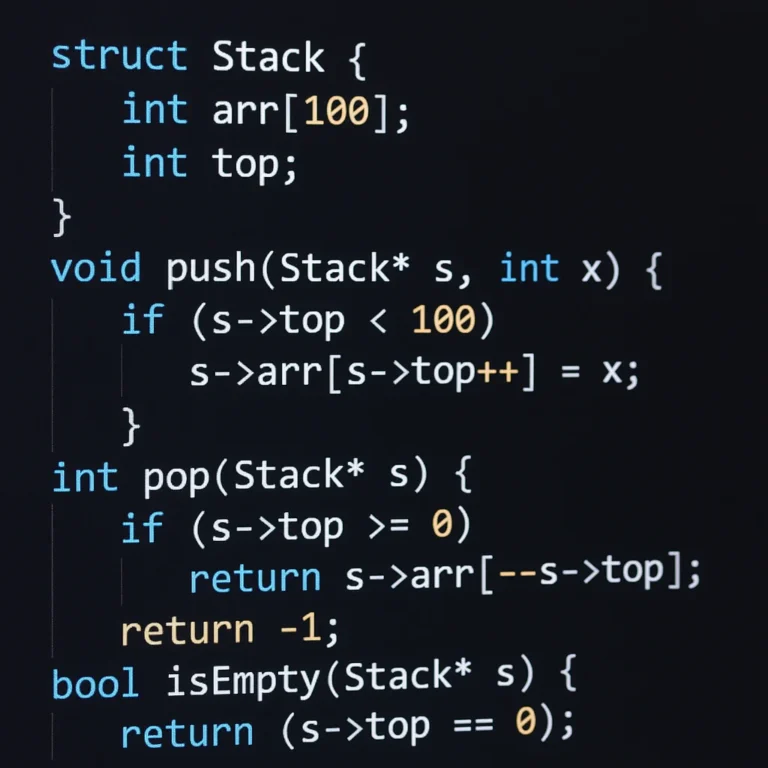
As we discuss in our guide to Back-End Technologies, the stack is managed by a Stack Pointer (SP). This is a small register in your CPU that tracks the “top” of the stack. When an underflow happens, the SP moves past the allocated boundary of the stack, pointing into “forbidden” memory territory.
💥 What Exactly Is Stack Underflow? A Deep Dive Into The Error
At its core, a stack underflow is a logic error. As the experts at Stack Overflow point out, “Stack underflow happens when you try to remove an element from an empty stack.”
But why is this so dangerous?
- Memory Corruption: If the system doesn’t immediately crash, it might return a value from a memory location that isn’t part of your stack. This “garbage data” can then be used in calculations, leading to catastrophic logic failures.
- Security Holes: Hackers love underflows. By forcing a stack to underflow, they might be able to redirect the program’s execution flow to a malicious script.
- System Instability: In embedded systems (like your car’s braking software or a microwave), a stack underflow isn’t just a bug; it’s a safety hazard.
🛠️ 7 Common Causes of Stack Underflow in Programming
Why does this happen to good developers? Here are the top 7 reasons we see at Stack Interface™:
- Unbalanced Push/Pop Operations: You pushed three items but tried to pop four. It’s basic math, but in a 10,000-line codebase, it’s easy to lose track.
- Incorrect Loop Conditions: A loop that executes one too many times, calling
pop()on the final iteration when the stack is already depleted. - Recursive Function Failures: While recursion usually causes overflows, a poorly managed “backtracking” algorithm can accidentally pop more states than it pushed.
- Malformed Transaction Data: Especially common in the Ethereum Virtual Machine (EVM). If a smart contract expects three arguments on the stack but only receives two, you get a “Stack Underflow.”
- Improper Error Handling: A function fails and returns early, but the code calling it assumes it pushed a result onto the stack.
- Direct Stack Pointer Manipulation: In C or Assembly, manually decrementing the Stack Pointer (SP) too far.
- Multi-threaded Race Conditions: One thread pops an item just as another thread was about to, leaving the second thread reaching for an empty stack.
🔍 How to Detect and Diagnose Stack Underflow Issues Efficiently
Detecting an underflow is like being a digital detective. You know something is wrong, but the “crime scene” (the crash) might happen long after the underflow occurred.
Step-by-Step Diagnosis:
- Step 1: Use a Debugger. Tools like GDB (GNU Debugger) allow you to set “watchpoints” on your stack pointer.
- Step 2: Check the Stack Pointer. If your SP value is higher (or lower, depending on architecture) than the stack’s base address, you’ve found your leak.
- Step 3: Log Every Operation. In development, wrap your
pop()calls in a logger.- Example:
if (stack.size == 0) { log_error("Underflow imminent!"); }
- Example:
- Step 4: Static Analysis. Use tools like Coverity to scan your code for paths where a pop might occur on an empty stack.
🧩 Stack Underflow vs. Stack Overflow: Key Differences Explained
Don’t get them twisted! Here is a quick comparison table to keep your head straight:
| Feature | Stack Overflow | Stack Underflow |
|---|---|---|
| Direction | Stack grows too large for its memory. | Stack is emptied, and a pop is attempted. |
| Primary Cause | Deep recursion or massive local variables. | Logic errors, unbalanced pops, malformed data. |
| Common Symptom |
java.lang.StackOverflowError or Segfault. |
Undefined behavior, “Stack Underflow” EVM error. |
| Analogy | Trying to put too many clothes in a suitcase. | Trying to take a shirt out of an empty suitcase. |
| Frequency | Very common (especially in recursion). | Less common, but often more difficult to debug. |
⚙️ Preventing Stack Underflow: Best Practices and Coding Tips
Prevention is better than a 3 AM debugging session. We recommend following these Coding Best Practices:
- The “Golden Rule”: Never, ever call
pop()without callingisEmpty()first. - Use Wrapper Classes: Instead of using raw arrays, use standard library containers like
std::stackin C++ orjava.util.Stackin Java, which often have built-in protections. - Unit Testing: Write tests specifically designed to “stress” your stack. What happens if you pop 100 times? What happens if you pop from a newly initialized stack?
- Assertions: Use
assert(stack.size() > 0)before pops during the development phase.
🔒 Security Risks and Vulnerabilities Linked to Stack Underflow
In the world of cybersecurity, a stack underflow can be a “trapdoor.” If an attacker can trigger an underflow, they might be able to read sensitive data that was previously stored in that memory location (a “Leaky Abstraction”).
In some cases, particularly in older systems or specific smart contract vulnerabilities, an underflow can lead to Privilege Escalation. If the stack pointer lands on a return address, the attacker could overwrite it to point to their own code.
🧪 Real-World Examples and Case Studies of Stack Underflow Bugs
The Cronus Zen Hardware Glitch
One of the most common “consumer” encounters with this error happens with the Cronus Zen, a popular gaming peripheral. Users often see a “Stack Underflow” message on the device’s OLED screen.
As seen in the featured video, this usually isn’t a coding error by the user, but a firmware hang-up.
- The Fix: A “Hard Reset.” You hold the two blue buttons while plugging in the power.
- The Perspective: The video creator notes that “the hard reset is the quickest way to fix errors” when the LEDs go red, green, and blue.
👉 Shop Cronus Zen on:
- Cronus Zen Controller Emulator: Amazon | eBay | Cronus Official
The Ethereum EVM Error
In the blockchain world, developers often ask, “Why do I get stack underflow when executing sendTransaction?”. This usually happens because the transaction data is malformed. If the EVM expects a certain number of items to be on the stack to complete an opcode (like ADD or SSTORE) and they aren’t there, the transaction fails instantly to protect the network.
🛡️ Tools and Debuggers for Managing Stack Underflow Errors
If you’re serious about squashing these bugs, you need the right gear. Here’s our “Stack Interface™ Approved” toolkit:
| Tool Name | Type | Best For |
|---|---|---|
| Valgrind | Memory Debugger | Detecting memory leaks and underflows in C/C++. |
| Truffle/Hardhat | Blockchain Suite | Debugging EVM stack errors in Solidity. |
| GDB | CLI Debugger | Low-level stack pointer inspection. |
| SonarQube | Static Analysis | Catching “pop-before-check” logic in CI/CD. |
👉 Shop Programming Tools on:
🎯 Optimizing Stack Usage to Avoid Underflow in Embedded Systems
In embedded development (think Arduino or specialized ARM chips), you don’t have the luxury of an OS protecting you. A stack underflow here can literally brick a device.
Expert Tip: Always initialize your stack with a “Magic Number” (like 0xDEADBEEF). If you check the memory address just below your stack base and that magic number is gone, you know an underflow occurred. This is a classic technique we use when optimizing Back-End Technologies for hardware.
📚 Stack Underflow in Different Programming Languages: C, Java, Python, and More
- C/C++: The Wild West. No safety nets. If you pop an empty stack, C will gladly give you whatever junk is in memory.
- Java: Much safer. The
Stackclass will throw anEmptyStackException. It’s noisy, but it prevents memory corruption. - Python: Similar to Java, calling
pop()on an empty list (Python’s de facto stack) raises anIndexError: pop from empty list. - Solidity (EVM): As mentioned, this is a “hard” error that reverts the entire transaction.
🤖 Automating Stack Underflow Detection with Static Analysis and CI/CD Pipelines
Why find bugs yourself when you can make a robot do it? Integrating AI in Software Development has made this easier than ever. Modern AI-driven linters can predict execution paths that lead to an empty stack.
We recommend adding a “Stack Depth Check” to your Jenkins or GitHub Actions pipeline. If the static analyzer sees a pop() without a preceding size() check, the build should fail. It’s tough love, but it works!
🧑💻 Developer Stories: How We Tackled Stack Underflow in Complex Projects
I remember a project at Stack Interface™ where we were building a custom physics engine for a mobile game. The character would randomly teleport to the coordinates (0,0) whenever they jumped near a wall.
We spent three days looking at collision logic. It turned out to be a stack underflow. Every time the character jumped, we pushed a “state” onto the stack. If they hit a wall, we popped it. But if they hit a specific corner, the code triggered two pops for one push. The second pop grabbed a null value from memory, which the engine interpreted as 0.
The lesson? Always log your stack size!
🔄 Handling Stack Underflow Gracefully: Error Recovery and Fallback Strategies
If an underflow happens, how should your app react?
- Fail Fast: In most cases, crashing is better than continuing with bad data.
- Graceful Degradation: In UI components, if a stack underflow occurs (like in an “Undo” stack), simply disable the “Undo” button and clear the error.
- Logging and Alerting: Ensure the error is sent to a service like Sentry so you can fix the root cause.
🚀 Advanced Topics: Stack Underflow in Multithreading and Concurrent Environments
This is where things get spicy. In a multithreaded environment, you might check isEmpty(), find it’s false, and then—before you can call pop()—another thread sneaks in and steals that last item.
This is a classic TOCTOU (Time-of-Check to Time-of-Use) bug. To solve this, you must use Atomic Operations or Mutex Locks. If you’re interested in how this applies to large-scale data processing, check out our section on Data Science.
But wait—if we lock the stack, do we risk a deadlock? And what happens if the stack underflow is actually a symptom of a much larger memory leak? We’ll wrap up these burning questions in our final thoughts.
Conclusion: Mastering Stack Underflow for Robust Software Development
Stack underflow may not get the same headlines as its boisterous sibling, stack overflow, but it’s no less critical to understand—especially if you’re developing apps or games where stability and security are paramount. From our experience at Stack Interface™, stack underflow is fundamentally a logic error that occurs when you try to pop from an empty stack, leading to undefined behavior, crashes, or even exploitable vulnerabilities.
Whether you’re debugging a quirky teleport bug in a physics engine or wrestling with Ethereum smart contract failures, the key takeaway is this: always validate your stack state before popping. Use the right tools, write comprehensive unit tests, and embrace static analysis and CI/CD pipelines to catch these errors early.
For hardware enthusiasts, devices like the Cronus Zen remind us that stack underflow isn’t just a software problem—it can manifest in firmware and embedded systems, requiring hard resets or firmware updates.
By following best practices, leveraging modern debugging tools, and understanding the nuances in different programming languages, you can not only prevent stack underflow but also gracefully handle it when it inevitably sneaks in.
So, next time you see that cryptic “Stack Underflow” error, you’ll know exactly what’s going on—and how to fix it. No more ghost hunting in your code!
Recommended Links for Further Learning and Shopping
-
Cronus Zen Controller Emulator:
Amazon | eBay | Cronus Official Website -
The C Programming Language (K&R), 2nd Edition:
Amazon | Walmart -
Debugging with GDB:
Amazon -
Valgrind Memory Debugger:
Official Site -
Truffle Suite for Ethereum Development:
Official Site -
Sentry Error Monitoring:
Official Site
Frequently Asked Questions (FAQ) About Stack Underflow
What causes stack underflow in app development?
Stack underflow typically arises when your code attempts to pop an element from an empty stack. This can happen due to unbalanced push/pop operations, incorrect loop conditions, or logic errors in recursive functions. In app development, especially games or embedded systems, this often results from failing to check if the stack is empty before popping, or from race conditions in multithreaded environments.
How can stack underflow affect game performance?
In games, stack underflow can cause unexpected crashes, erratic behavior (like teleporting characters or corrupted game states), and even security vulnerabilities if exploited. Since games often rely on stacks for managing states, undo operations, or scripting engines, an underflow can lead to corrupted memory reads, causing glitches or freezes that degrade user experience.
What are common symptoms of stack underflow errors in programming?
Common symptoms include:
- Program crashes or segmentation faults.
- Unexpected or nonsensical output.
- Silent logical errors where variables hold garbage values.
- Specific error messages in managed languages (e.g.,
EmptyStackExceptionin Java). - Transaction failures in blockchain environments with “stack underflow” errors.
How do developers prevent stack underflow in mobile apps?
Developers prevent stack underflow by:
- Always checking if the stack is empty before popping.
- Using safe, built-in stack implementations from standard libraries.
- Writing unit tests that simulate edge cases, like popping from an empty stack.
- Employing assertions during development to catch underflow conditions early.
- Utilizing static analysis tools integrated into CI/CD pipelines to detect risky code paths.
What debugging techniques help identify stack underflow issues?
Effective debugging techniques include:
- Using debuggers like GDB to monitor the stack pointer and stack size.
- Logging stack operations to trace when underflow might occur.
- Running static analysis tools such as Coverity or SonarQube.
- Employing memory debuggers like Valgrind to detect invalid memory access.
- Simulating transactions or function calls in sandbox environments (e.g., Remix IDE for Ethereum).
Can stack underflow lead to security vulnerabilities in games?
Absolutely. Stack underflow can cause memory corruption, which attackers might exploit to execute arbitrary code or escalate privileges. In games, this could mean cheating, data theft, or crashing multiplayer servers. Ensuring robust stack management is a critical part of secure game development.
What programming languages are most prone to stack underflow problems?
Languages like C and C++ are most prone because they provide direct memory management without built-in safety checks. Languages like Java and Python handle stack underflow more gracefully by throwing exceptions. However, custom stack implementations or low-level extensions in any language can still suffer from underflow if not carefully managed.
Reference Links and Authoritative Resources
-
Stack Overflow discussion on provoking stack underflow in C:
https://stackoverflow.com/questions/47154336/provoke-stack-underflow-in-c -
Ethereum Stack Exchange on stack underflow in sendTransaction:
https://ethereum.stackexchange.com/questions/28795/why-do-i-get-stack-underflow-when-executing-sendtransaction -
Official Cronus Zen Website:
https://www.cronusmax.com/ -
GNU Debugger (GDB) official site:
https://www.sourceware.org/gdb/ -
Valgrind Memory Debugger:
https://valgrind.org/ -
Coverity Static Analysis:
https://www.synopsys.com/software-integrity/static-analysis-sig/coverity.html -
Ethereum Virtual Machine (EVM) Documentation:
https://ethereum.org/en/developers/docs/evm/ -
OWASP Smart Contract Security Verification Standard:
https://owasp.org/www-project-smart-contract-security-verification-standard/ -
Sentry Error Monitoring:
https://sentry.io/
With these insights and tools in your arsenal, you’re well-equipped to conquer stack underflow errors and build more robust, secure, and performant applications and games. Happy coding! 🚀